How to Set Up Passkeys: A 2026 Step-by-Step Guide
You probably have somewhere between 80 and 200 online accounts, and almost every one of them is still protected by a string of characters you have to memorize, paste, or pray your password manager autofills correctly. That model is finally on its way out.
Learning how to set up passkeys on the accounts you already use is the single highest-impact security upgrade most consumers and small businesses can make in 2026 — and it’s free.
Passkeys replace passwords with a pair of cryptographic keys generated on your device. The “secret” half never leaves your phone, laptop, or hardware security key, which means there is nothing for a phishing site to steal, no leaked-database password to crack, and no shared secret to type into a fake login screen.
Google reports more than 800 million accounts are now using passkeys, Amazon added 175 million users in the technology’s first year, and 87% of companies surveyed by the FIDO Alliance are deploying or planning passkey support. This guide walks you through what passkeys are, why they’re so much safer than passwords, and exactly how to set them up on the accounts that matter most.
What Is a Passkey, in Plain English?
A passkey is a digital credential built on top of a long-established authentication standard called WebAuthn, governed by the FIDO Alliance. When you create a passkey for a website or app, your device generates two mathematically linked keys:
- A public key, which the website stores in your account record. This key cannot be used to sign in.
- A private key, which never leaves your device’s secure hardware (the Secure Enclave on iPhones and Macs, the TPM or StrongBox on Android, or a hardware security key like a YubiKey).
When you go to log in, the site sends a one-time challenge. Your device proves it holds the private key by signing the challenge — but only after you authorize it with Face ID, Touch ID, Windows Hello, or your device PIN. The signed response goes back to the site, which verifies it against the public key on file. You’re in. No password was typed, transmitted, or stored on a server, so there is nothing for an attacker to steal.
Why Passkeys Are Dramatically Safer Than Passwords
Modern phishing kits, credential stuffing attacks, and brute-force GPU rigs all exploit the same fundamental weakness: passwords are shared secrets. Passkeys eliminate the shared secret entirely, which collapses several attack categories at once.
Phishing Becomes Impossible
A passkey is cryptographically bound to the exact domain that created it. If an attacker sends you a fake “Microsoft” login page at micros0ft-login.com, your passkey will simply refuse to fire — there is no muscle-memory mistake to exploit. Compare that to a password, which you can be tricked into typing anywhere.
Database Breaches Stop Mattering
When a website is breached, the only thing the attacker steals from your account is the public key — which is, by design, useless without the matching private key locked in your device. The era of “your password was leaked, change it everywhere you reused it” is fading fast for any account where passkeys are enabled.
The data-protection logic we covered in our piece on why protecting your personal data matters applies double here: passkeys reduce the blast radius of every breach.
Brute Force Is Off the Table
A standard consumer-grade GPU in 2026 can crack an 8-character password in roughly 12 minutes. Passkeys use 2048-bit RSA or 256-bit elliptic curve cryptography. There is no offline cracking attack against them at all.
No More Password Reuse Risk
Every passkey is unique to the site it was created for. There is no possibility of “reusing” a passkey, which silently fixes the most common consumer mistake — the same password on a dozen sites.
The combined effect is large. The FIDO Alliance reports that organizations rolling out passkeys see account-takeover attacks drop by more than 90% within the first year.
What You Need Before You Start
You don’t need new hardware to use passkeys, but you do need a reasonably modern device:
- iPhone or iPad: iOS or iPadOS 16 or later
- Mac: macOS Ventura (13) or later
- Android phone or tablet: Android 9 or later, with screen-lock enabled
- Windows PC: Windows 10 or 11 with Windows Hello configured (PIN, fingerprint, or facial recognition)
- A passkey “vault”: Apple Passwords (formerly iCloud Keychain), Google Password Manager, Microsoft Authenticator, or a third-party manager like 1Password, Bitwarden, or Dashlane
Decide upfront where you want your passkeys stored. Apple, Google, and Microsoft each sync passkeys to their own ecosystems, which is convenient if you live in one — but a cross-platform manager like 1Password or Bitwarden is the better choice if you mix iPhone with a Windows PC or use multiple browsers. The choice mainly affects sync, not security; the cryptography is the same in every case.
How to Set Up Passkeys on Your Most Important Accounts
You don’t need to migrate every account at once. Start with the accounts that, if compromised, would cascade into other compromises — your email, your password manager, your financial logins, and your work accounts. Here is the typical flow on each major service.
- Sign in to your Google Account at myaccount.google.com.
- Open Security from the left navigation, then choose Passkeys and security keys.
- Click Create a passkey. Google will detect your current device and ask you to authorize with biometrics or your screen lock.
- Confirm the new passkey appears in the list. Repeat on any other device you use regularly so you have a backup.
Apple ID
If you’re on an Apple device with iCloud Keychain enabled, your Apple ID and any site you sign into using “Sign in with Apple” already use passkey-style authentication automatically. To explicitly create or manage passkeys, open Settings → Passwords on iPhone or System Settings → Passwords on Mac, then add new passkeys per site as you visit them.
Microsoft (including Microsoft 365 and Outlook.com)
- Sign in at account.microsoft.com.
- Open Security → Advanced security options.
- Under Ways to prove who you are, choose Add a new way to sign in or verify → Use a passkey.
- Authenticate with Windows Hello, Touch ID, or your phone, and follow the prompts.
Amazon, GitHub, PayPal, eBay, and Most Major Retailers
Look for “Passkey” or “Sign in faster with a passkey” inside Account → Login & Security. The setup wizard is essentially the same: confirm with biometrics, name the passkey (e.g. “iPhone 15 — Personal”), and save. Hundreds of services have shipped passkey support over the past 18 months; if you don’t see it on a site you use, check our cybersecurity facts roundup in a few months — the list grows weekly.
Your Password Manager Itself
If you use 1Password, Bitwarden, or Dashlane, enable a passkey for the manager’s own login. This is the highest-leverage account in your life, because it gates every other credential. Keep a printed recovery code in a safe place.
Spot the Scam. Level Up.
Real scenarios. Split-second calls. Become harder to fool with every round.
Passkeys for Small Businesses
Passkeys aren’t just a consumer feature. For small businesses, they shut down two of the three most damaging attacks against SMBs: phishing-driven account takeover and credential-stuffing logins from old breach data. Roll them out in this order:
1. Start with Microsoft 365 or Google Workspace
Both platforms now support passkeys for end-user logins and admin accounts. Enable passkeys in your tenant settings, require them for global admins first, then expand to all staff. Pair this with conditional access policies that block legacy authentication protocols, since those bypass passkey enforcement.
2. Issue Hardware Keys to Critical Roles
For finance, IT admin, and executive accounts, supplement device-bound passkeys with a physical FIDO2 hardware key (YubiKey, Google Titan, or equivalent). Store one in the office safe and one with the user. Hardware keys provide a passkey that cannot be exfiltrated even if the device is compromised — the strongest authentication available today.
3. Document a Recovery Plan
The most common passkey mistake at small companies is forgetting recovery. If an employee loses every device that holds a passkey, you need a defined process: backup codes printed and stored, an admin-driven account reset, or a secondary registered hardware key. Write it down before you need it.
4. Train and Simulate
A 20-minute lunch-and-learn covers the basics for most teams. Reinforce the training with realistic exercises — for example, our scam detection challenge and cyber trivia game are quick ways to keep awareness sharp without adding meeting load.
Common Questions and Sticking Points
What If I Lose My Phone?
If your passkeys are synced through iCloud Keychain, Google Password Manager, Microsoft Authenticator, or a cross-platform manager, they’re already on your other registered devices and in encrypted backup. Sign in to a replacement device using your platform account and your passkeys reappear after biometric verification. If you used a hardware key with no sync, your spare is your recovery — which is why you keep two.
Are Passkeys Truly Phishing-Proof?
For the website that issued the passkey, yes. Attackers cannot trick the device into authenticating against a look-alike domain. They can still try to phish you for password-based fallbacks, recovery codes, or one-time SMS codes, which is why turning off SMS as a fallback (where possible) is a smart follow-up step.
Can I Use the Same Passkey on Two Devices?
Sort of. Each device generates its own passkey for a given site, but they all sync into your chosen vault, so the user experience feels seamless. Sharing a passkey across people (e.g. a household Netflix login) is supported by managers like 1Password using shared vaults. Each person still authenticates with their own biometrics.
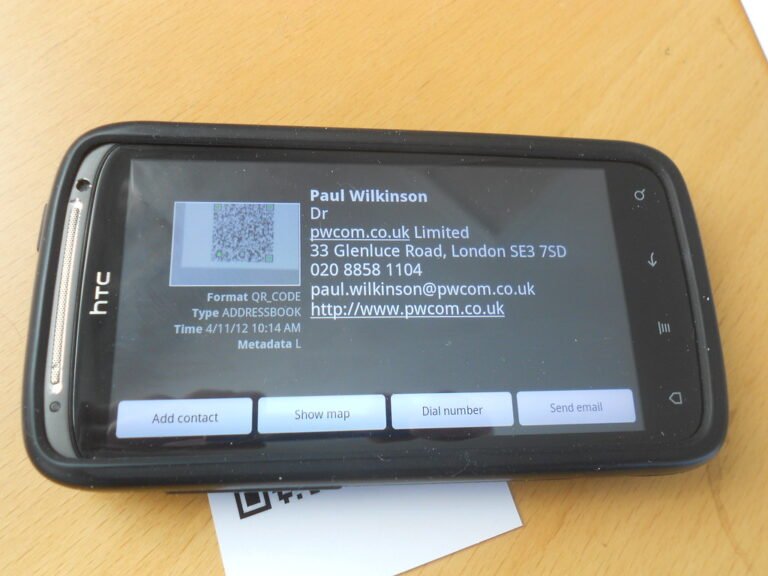
What About Public or Shared Computers?
You can use a passkey from your phone to sign in on a borrowed laptop using a temporary QR-code-based “cross-device” flow. The phone does the cryptography; the laptop never sees a private key. It’s especially handy in libraries, hotels, and conference rooms — and far safer than typing a password on a machine that might log keystrokes. (For more on shared-network risk, see our guide to public Wi-Fi safety.)
Should I Delete My Old Passwords?
Not yet. Until every site offers passkeys — which the FIDO Alliance estimates is 18 to 24 months out — keep your password manager populated and your existing credentials strong. The transition is gradual; most people will hold a hybrid setup through 2027.
The Bottom Line
Passkeys are the rare security upgrade that is simultaneously easier to use and harder to defeat. They eliminate phishing of the credential, neutralize most database breaches, and free you from inventing yet another 16-character password you’ll instantly forget. The technology is real, mainstream, and supported by the platforms most consumers and small businesses already rely on every day.
Test your digital defenses
Take the Cyber Security Trivia challenge — 10 rapid questions across passwords, phishing, Wi-Fi, malware, and more. Find out where your knowledge is solid and where it needs work.
Start the quiz →If you do nothing else this week, set up a passkey on your primary email account. That single change protects the inbox that controls every other “forgot password” flow in your digital life. Once that’s done, walk through the same process on your password manager, your bank, and your work account.
For more practical, jargon-free security upgrades, check out additional reading on the FIDO Alliance’s official passkeys page and the CISA Secure Our World consumer guides — and don’t miss our scam detector app walkthrough for adding another layer of friction against attackers who try to bypass your shiny new logins.