Faraday Bags, RFID Sleeves, and Travel VPNs: Real Tools That Stop Real Threats
Walk into any airport gift shop or scroll Amazon for “travel security gear” and you’ll find a wall of products promising to stop hackers cold: RFID-blocking wallets, Faraday pouches, anti-skim sleeves, anti-stalker phone cases, “spy-proof” backpacks.
Some of these tools are genuinely useful. Others are pure security theater — products that solve threats that barely exist while feeling reassuring at the cash register. The challenge for normal travelers is that the marketing for both categories looks identical.
This guide cuts through the noise. We’ll separate the gear that actually stops documented threats from the products that are mostly marketing, explain when each tool is worth carrying, and walk through a realistic kit that fits in one zippered pocket.
The framework is simple: every recommendation has to point to a real, documented attack pattern. No “what if a hacker…” scenarios. No imaginary threats. Just the gear that solves problems travelers actually have.
The “Threat Hierarchy” Before You Buy Anything
Travel security gear gets useful when it’s matched to the right threat. Here’s the rough hierarchy of risks that gear can address, ordered from most-likely to least-likely:
- Public Wi-Fi snooping at hotels and airports — extremely common, well-documented, easily mitigated with a VPN.
- Skimmer/shimmer attacks at compromised POS and ATM terminals — common in tourist areas, mitigated with tap-to-pay and good payment hygiene.
- Lost or stolen physical devices — laptop, phone, passport — by far the most likely incident on any trip, mitigated with strong device encryption and lockable bags.
- Key-fob relay attacks on cars left at the airport — real but uncommon, mitigated with a Faraday pouch.
- Live RFID skimming of contactless cards — heavily marketed, almost no documented real-world cases.
Notice the order. The single best gear investment for most travelers is a reputable VPN subscription. Faraday bags solve real but narrower problems. RFID-blocking wallets are the most marketed and the least useful. Build your kit accordingly.
VPNs: The One Tool Every Traveler Should Have
A reputable Virtual Private Network (VPN) creates an encrypted tunnel between your device and a trusted server, preventing anyone on the same Wi-Fi network from reading your traffic. Hotel and airport networks remain among the top three attack vectors for traveler data theft in 2026, and a VPN is the single highest-leverage countermeasure available.
What a VPN actually protects you against
A VPN encrypts your traffic from device to VPN server, meaning anyone on the same hotel Wi-Fi cannot read your usernames, passwords, banking session tokens, or unencrypted data. It also masks your real IP address from the websites you visit, which has secondary privacy benefits.
For a deep dive on why public Wi-Fi is so risky in the first place, see our guide on the risks of using public Wi-Fi — it explains the specific snooping techniques a VPN defeats.
What to look for in a travel VPN
The market is crowded; most are mediocre and a few are excellent. The features that actually matter for traveler use:
- A “kill switch” that cuts internet traffic if the VPN drops. Without this, your real connection briefly leaks if the tunnel disconnects — a common failure mode on weak hotel Wi-Fi.
- DNS leak protection so your DNS queries are routed through the VPN, not your ISP or hotel.
- Strong protocol support — WireGuard or OpenVPN. Avoid VPNs that only offer older, weaker protocols.
- Independently audited no-logs policy. A VPN that logs your activity defeats most of the privacy benefit.
- A reputable corporate parent. Free VPNs are usually ad-supported or worse — some have been caught selling user data.
NordVPN, ExpressVPN, Mullvad, and Proton VPN consistently rank well in independent reviews and have audited no-logs claims. Avoid free VPNs and any service whose ownership is opaque.
Travel routers (the next-level option)
For frequent travelers, a small travel router with built-in VPN support adds another layer. The router connects to the hotel Wi-Fi once, runs a VPN tunnel for everything behind it, and creates a private network for your devices. Benefits: your laptop, phone, and tablet all use the encrypted tunnel without configuring each individually, and “captive portal” sign-in screens stop being a hassle. Tradeoff: an extra small device to pack and configure.
Faraday Bags: The Real Use Cases
A Faraday bag is a fully enclosed, conductive-mesh-lined pouch that blocks all radio frequencies — Wi-Fi, Bluetooth, cellular, GPS, NFC, and anything else. They’re not the same as RFID-blocking wallets (more on those below). Quality Faraday bags provide 60–80 dB of attenuation, which is enough to make the contents radio-silent. Here are the real use cases.
Stopping car key-fob relay attacks
Modern proximity-keyfob cars (most luxury and many mainstream models) are vulnerable to relay attacks: criminals use two devices to amplify the fob’s signal from inside your house out to the driveway, tricking the car into thinking the key is present and unlocking it. The attack is real, documented across multiple police agencies, and rising. The fix is brutally simple: keep the key fob in a Faraday pouch. No signal in, no signal out, no relay attack. If you leave a car at the airport during a trip, store the spare fob in a Faraday pouch at home; if you’re a hotel valet customer, ask the valet to keep your fob in your provided Faraday pouch.
Sleeping the phone for true off-grid moments
Powering a phone off doesn’t always disable all radios — modern devices still ping for tracking and emergency signals. A phone in a Faraday bag is genuinely off the network. Useful for high-stakes meetings, sensitive conversations, journalists working in restricted regions, or simply guaranteed device privacy at a security checkpoint.
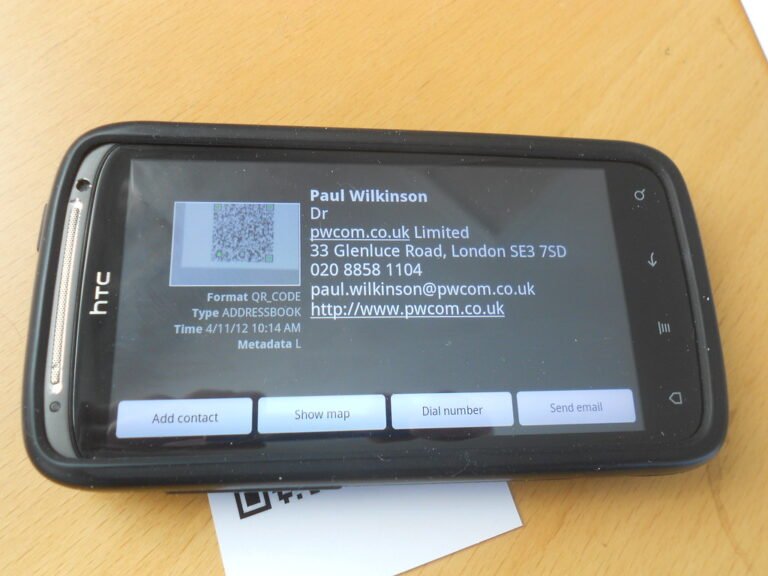
Travel passport sleeve (limited but real)
Modern U.S. passports include an RFID chip that can be read at very short range. A Faraday-grade passport sleeve makes the chip unreadable until removed. The risk of a passport being remote-read is small in practice, but a $15 sleeve is a reasonable belt-and-suspenders measure for frequent international travelers.
RFID-Blocking Wallets: Mostly Marketing
This is the gear category most heavily promoted to travelers and the one with the weakest evidence base. Here’s the honest picture.
The threat is mostly theoretical. Despite a decade of warnings about contactless-card “skimming” by criminals walking by with concealed readers, law enforcement reports virtually no documented real-world cases of this attack succeeding in the wild. Modern EMV contactless cards generate one-time cryptographic tokens for each transaction; even if a thief read your card at range, the data wouldn’t include the CVV or PIN, and the captured data couldn’t be replayed.
Most “RFID-blocking” wallets only partially work. Lab testing shows aluminum-construction wallets reliably block contactless reads, but foil-lined wallets pass tests only about 50% of the time. The same protection effectively comes free with a thicker leather wallet that holds two or more cards together — the cards’ overlapping antennas already disrupt clean reads.
The legitimate niches. If you carry an older corporate access badge, certain hotel keycards that use weakly encrypted RFID, or a pre-EMV contactless card from a smaller issuer, blocking can matter. For modern Visa/Mastercard tap-to-pay, it usually doesn’t.
Verdict: If you want one for peace of mind, buy a quality aluminum-construction wallet. Don’t pay a premium for “RFID-blocking” branding on a leather wallet you’d buy anyway. The marketing premium is the actual scam here.
The “Realistic Travel Security Kit”
Here’s a balanced kit that fits in a small pouch and addresses the actual threats most travelers face. Total cost: ~$80–$200 depending on choices, mostly the VPN subscription.
- Reputable VPN subscription ($60–$100/year). Set up before you leave. Test it on hotel Wi-Fi the first night.
- Quality Faraday pouch for car key fob ($15–$30). Keep the fob in it whenever the car is parked at the airport or hotel.
- Travel router with built-in VPN support ($40–$80). Optional but a major convenience for anyone bringing multiple devices.
- USB data blocker ($10). Plugs between a public USB charging port and your cable, blocking the data pins so only power flows. Stops “juice-jacking” attacks at airports and rental cars.
- RFID-blocking passport sleeve ($10). Cheap insurance for the small but non-zero remote-read risk on biometric passports.
- Lockable cable or small portable safe ($25–$60). Locks your laptop or valuables to a hotel-room fixture. Far more useful than any RFID gear because device theft is a real, common travel risk.
Not on the list: branded “anti-hacker” backpacks, dramatic-looking tactical wallets, GPS-jammers (illegal in most countries), and anything labeled “military-grade” without independent testing data. Marketing language is not a feature.
Setting Up Each Tool in Under an Hour
Buying gear isn’t enough. Here’s the day-before-departure setup that makes each tool actually useful.
VPN setup (30 minutes). Install the app on every travel device — phone, tablet, laptop. Sign in. Test by connecting to a server in your home country; verify you can browse normally. Enable the kill switch and DNS leak protection in settings. Save a couple of nearby server locations as favorites for fast switching.
Travel router setup (20 minutes). Configure once at home. Connect the router to your home Wi-Fi temporarily, enter your VPN credentials, save the configuration. At the hotel, you’ll only need to enter the hotel network credentials once.
Faraday pouch test (5 minutes). Put your phone in the bag. Try to call it. If it rings, the pouch isn’t sealed properly or doesn’t provide enough attenuation — return it.
Device encryption check (10 minutes). Confirm full-disk encryption is enabled on every laptop and full device encryption on every phone. The single most useful protection against device theft is a strong password plus encryption — not gear.
Frequently Asked Questions
Do I really need a VPN if I always use my phone’s hotspot instead of hotel Wi-Fi?
Less urgent, but still useful. Cellular networks have their own snooping risks (less common, but rogue cell sites do exist), and some apps still leak metadata that a VPN protects. Plus, your phone’s data plan might be expensive abroad — hotel Wi-Fi plus a VPN is cheaper than international roaming for most people.
Are free VPNs ever okay?
For brief, low-stakes use, maybe. For sensitive activity (banking, email, work), no. Free VPNs are usually subsidized by advertising, data sales, or worse. The exception is reputable freemium tiers from paid providers (Proton VPN’s free tier is often cited as legitimate), but for travel use you want the paid tier’s full feature set.
Will a Faraday bag damage my phone or credit cards?
No. Faraday bags block radio signals; they don’t generate any. The phone or cards inside continue to function normally — they just can’t communicate while inside the bag. Magnetic-stripe cards and magnetic-stripe-only items also aren’t affected.
What about anti-spy phone screens or “privacy filters”?
These have a real but narrow use case: preventing shoulder-surfing in tight quarters (planes, trains, crowded cafés). They don’t stop hackers, malware, or remote attacks — only direct visual snooping. Worth $20–$30 if you frequently work on sensitive documents in public.
Can a VPN slow down my connection enough to be annoying?
A small slowdown is normal — usually 5–20%. A reputable VPN on a server in or near your country should not be dramatically slower than the underlying connection. If it is, switch to a different server location or a better protocol (WireGuard is generally faster than OpenVPN). Hotel Wi-Fi is usually the bottleneck, not the VPN.
The Bottom Line: Buy the Tools That Match the Threats
The travel security industry is full of products that look impressive and solve nothing. The ones worth carrying are the ones that match documented attack patterns: a reputable VPN for the very real threat of public Wi-Fi snooping, a Faraday pouch for the real but narrower risk of relay attacks on car keys, a USB data blocker for the small but specific juice-jacking risk, and lockable storage for the most likely incident of all — a stolen device.
Skip the marketing-driven “tactical” wallets and assume any product whose primary feature is its own branding is selling reassurance, not protection.
Want to keep treating your data as the asset it is after you arrive? Subscribe to the Making Sense of Security newsletter for ongoing, practical security briefings written for normal humans who travel, work, and live online — not the security-industrial complex.