Hotel and Airport Wi-Fi: Why It’s Worse Than You Think and How to Use It Safely
You connect to the airport Wi-Fi to check email while you wait for your flight. The captive portal asks for your name and email to “verify access,” then drops you onto a normal browsing experience. You log into your bank’s app to confirm a charge.
You answer a Slack message from work. You scroll your inbox. You feel productive — and you’ve just walked into one of the most common, lowest-effort, highest-yield attacks targeting travelers in 2026. The “free Wi-Fi” you joined wasn’t the airport’s. It was an Evil Twin set up by a criminal sitting two gates away, and your bank session, work credentials, and email content all just flowed through their device.
Hotel and airport Wi-Fi are the backbone of business and leisure travel — and the attack surface most travelers underestimate. The good news: a small set of habits, anchored by a reputable VPN, makes these networks safe to use even when they’re hostile.
The bad news: most travelers don’t have those habits, and the criminal economy around traveler-targeted Wi-Fi attacks is bigger and more sophisticated than ever. This guide walks through exactly what’s happening on those networks, the specific 2026 attack patterns, and the practical playbook that turns “free hotel Wi-Fi” from a risk into a routine convenience.
What’s Actually Happening on Hotel and Airport Wi-Fi
Most public Wi-Fi networks are designed for convenience, not security. The architecture itself creates exposure that doesn’t exist on your home network or your cellular connection. Here’s the core picture.
Shared broadcast medium. Wi-Fi is radio. Every device on the network can potentially see every other device’s traffic. On modern networks with WPA3 client isolation, this is mitigated — but many hotels and airports run older WPA2 or open networks where isolation is weak or absent.
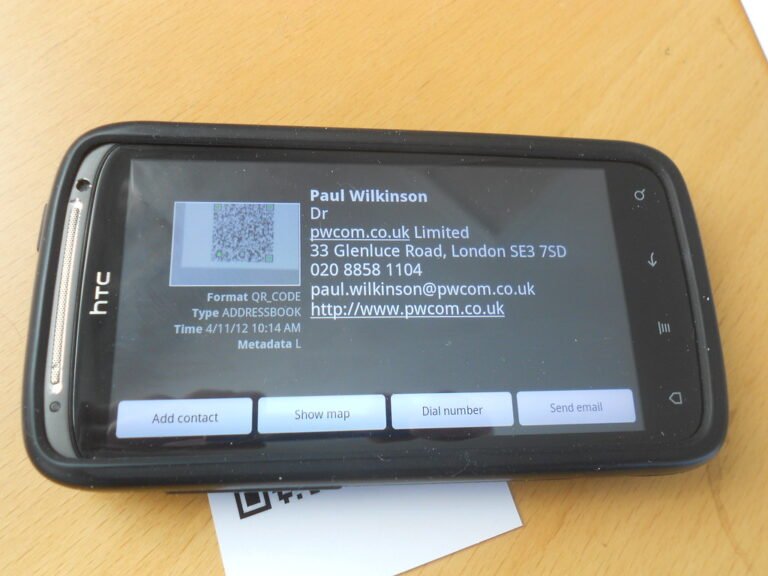
Captive portal interception. The “click to accept terms” page that appears when you first connect is a captive portal. Legitimate ones drop you onto the real internet after you accept. Malicious ones impersonate the real page, harvest credentials, or redirect to phishing sites. You can’t tell the difference visually.
DNS-level redirection. Even after you’re “connected,” the network controls the DNS server that translates domain names into IP addresses. A malicious network can redirect “yourbank.com” to a phishing-page IP and serve a perfect replica of your bank’s login page. HTTPS plus certificate validation defeats this in modern browsers — but only if you notice the certificate warning and stop.
Man-in-the-middle (MITM) interception. A criminal with control of the network can intercept and modify some traffic in real time. Encrypted traffic (HTTPS) is harder to intercept but not impossible — especially against users who click through certificate warnings or who use older, vulnerable apps.
The Three Attack Patterns Travelers Encounter Most
Evil Twin Networks
An “Evil Twin” is a Wi-Fi network whose name (SSID) imitates a legitimate one — “Marriott_Guest” near a Marriott, “American_Airlines_Free” near an American gate, “Starbucks_WiFi” anywhere. The criminal’s portable hotspot broadcasts a stronger signal than the real network from a closer distance, so devices auto-join the criminal’s network instead.
Real-world case: An April 2024 arrest in Australia documented a man who set up Evil Twin networks at airports in Perth, Melbourne, and Adelaide specifically to harvest email and social-media credentials from travelers. The attack worked at scale because most travelers can’t distinguish between the legitimate airport network and the impostor.
Defense: Confirm the exact network name with hotel staff or printed signage. Disable Wi-Fi auto-join for unknown networks. Forget public networks immediately after use so your phone doesn’t auto-rejoin them on a future visit. Run a VPN — even on the legitimate network — so your data is encrypted regardless of who controls the access point.
Fake Captive Portal
You connect to a hotel network and see a login page asking for your room number, last name, and email. Or it asks you to “create an account” with a password. Or it requests your credit card to “verify access.” Some of these are legitimate; some are pure phishing pages designed to harvest data they then use against you.
2026 variations: Fake captive portals that ask for passwords matching common banking, email, or work-account formats. Portals that redirect to “complete your profile” pages requesting full identity information. Portals that demand a small “verification fee” via credit card — pure scam.
Defense: Real hotel and airport portals never ask for passwords from external services. They never charge a fee at the entry gate (any access fee is paid via the hotel’s billing system, not entered on a captive portal). They never ask for your full identity to grant Wi-Fi access. If the portal is asking for any of these, you’re on a fake.
DNS Spoofing and HTTPS Downgrade
A more sophisticated attacker controlling a network can serve fake DNS responses, redirecting requests for legitimate sites to attacker-controlled IPs. Combined with HTTPS-downgrade attacks (forcing your browser to connect over HTTP instead of HTTPS), this can serve fake login pages for sites you trust.
Defense: Modern browsers warn loudly about certificate problems and HTTP-only sites for sensitive services. Never click through a certificate warning, especially on public Wi-Fi. Use a VPN to encrypt DNS queries (most reputable VPNs route DNS through their own servers, defeating the network-level spoofing). Use DNS over HTTPS (DoH) in your browser settings as a defense in depth.
The “Hotel Wi-Fi Safety Routine”
Run this every time you arrive at a new hotel or hostile-network environment. Takes about two minutes; bulletproofs your session.
- Confirm the network name with staff before connecting. Don’t trust the name displayed in your phone’s Wi-Fi list. Ask the front desk for the exact name they use. If two networks with similar names appear, the front desk’s confirmed answer is the only authoritative source.
- Connect with VPN already running. Engage your VPN before joining the network. Many VPN apps support an “auto-connect on untrusted Wi-Fi” feature — enable it. The VPN encrypts everything, so even if the network is malicious, your traffic is unreadable.
- Verify the captive portal carefully. The login page should ask only for credentials related to your hotel stay (room number, last name) — never for external account passwords or extra payment.
- Use HTTPS-only browser modes. Both Chrome and Safari support “Always use HTTPS” or “HTTPS-only mode.” Enable it. The browser will refuse insecure connections to any site, defeating most network-level attacks.
- Keep DNS through your VPN. Most reputable VPNs route DNS through their servers by default. Confirm in settings that DNS leak protection is enabled.
- Forget the network when you check out. Long-press the network in your Wi-Fi list and “Forget this network.” This prevents your device from auto-joining a similarly named network at a future location.
// MISSION: TEST YOUR DEFENSES //
Passwords, phishing, Wi-Fi, malware. Six fronts. One quiz. Ten questions to prove it.
What’s Actually Safe on Hotel Wi-Fi (With a VPN)
With a reputable VPN engaged, the threat model changes dramatically. Here’s what’s safe and what to still avoid.
Safe with VPN: Browsing the web. Streaming video. Watching news. Reading email. Logging into accounts that use modern HTTPS and have 2FA enabled. Slack, Microsoft Teams, Zoom, and other modern collaboration tools. Most modern banking apps (which use additional certificate pinning beyond standard HTTPS).
Mostly safe with VPN, but use cellular if convenient: First-time logins to high-value accounts. Wire transfers. Tax-related logins. Account password changes. These work with a VPN, but the safer default is to switch to cellular data for the duration of the high-stakes activity.
Use cellular always: Initial banking app activation on a new phone. Account-recovery flows. Government portal access (IRS, Social Security). Use cellular data, your phone’s hotspot, or wait until you’re on a trusted network.
Specific Hotel and Airport Network Hazards
Pay-walled hotel Wi-Fi tiers
Many hotels offer “basic” free Wi-Fi and “premium” paid tiers that allegedly include security features. Don’t pay for the upgrade — bring your own VPN. The hotel’s “premium” Wi-Fi is rarely meaningfully more secure than the basic version, and it definitely doesn’t replace the protection a VPN provides.
Conference and event Wi-Fi
Networks at trade shows, conferences, and large events are particularly risky targets — high concentration of business travelers, often with corporate data on devices. Treat conference Wi-Fi the same as hotel Wi-Fi: VPN engaged, sensitive activity on cellular, no exceptions for “convenience.”
Long-haul airport gate Wi-Fi
Airports are the highest-density travel-target environment. Long-haul gates with international travelers are the richest hunting ground. The Australian Evil Twin case happened in airports specifically because the dwell time and target value are higher than almost any other location.
Coffee shops and chain restaurant Wi-Fi
Lower-stakes than hotels for short visits, but the same principles apply. The classic Starbucks, McDonald’s, and chain-restaurant Wi-Fi networks are well-known Evil Twin targets, especially in tourist neighborhoods.
The “Use My Cellular Instead” Rule
For any genuinely sensitive activity, the safest network is your own. Modern cellular data plans, especially on eSIM travel plans abroad, are dramatically cheaper than a few years ago — and they sidestep every public Wi-Fi attack pattern entirely.
The rule: If you’re about to log into your bank, change a password, send a wire transfer, or access government services, switch to cellular. Tether your laptop to your phone if needed. The cost is a few cents of data; the savings is “didn’t get phished on hotel Wi-Fi.”
For frequent travelers, an unlimited international eSIM plan from Airalo, Holafly, or Nomad (~$30–$60 for a few weeks) is a worthwhile investment. It sidesteps hotel Wi-Fi entirely for everything that matters.
Frequently Asked Questions
Is hotel Wi-Fi safer than airport Wi-Fi?
Marginally — hotels have somewhat better physical security and lower target density per square foot. But the threat patterns are essentially identical, and the same defenses apply. Treat both with VPN-on-by-default.
What if my VPN doesn’t work on the hotel network?
Some hotels block VPN protocols at the network level — usually accidentally, sometimes intentionally for “performance management.” Workarounds: try a different VPN protocol (WireGuard if you were on OpenVPN, or vice versa), use the VPN’s “stealth” or “obfuscation” mode if available, or fall back to cellular. Don’t proceed with sensitive activity on Wi-Fi without a working VPN.
Are HTTPS websites safe even without a VPN on hotel Wi-Fi?
Mostly, but not completely. HTTPS encrypts the page contents, but DNS lookups, traffic patterns, and metadata can still leak. Captive portal phishing and DNS spoofing can sidestep HTTPS in some scenarios. A VPN closes the remaining gaps. Treat HTTPS-without-VPN as “better than HTTP” but not as “safe.”
Should I disable Wi-Fi entirely while traveling?
For a short trip, possibly — your eSIM cellular plan handles most use cases. For longer trips with lots of data needs, Wi-Fi-with-VPN is the practical balance. Either way, disable auto-join for unknown networks and forget hotel Wi-Fi after each stay.
What’s the single biggest mistake travelers make on hotel Wi-Fi?
Not running a VPN. Every other mistake is downstream of this one. The VPN turns hostile networks into safe ones. (Read more on the broader public Wi-Fi risk picture in our guide to the risks of using public Wi-Fi.)
The Bottom Line: Hotel Wi-Fi Is a Solved Problem (If You Bring the Solution)
Hotel and airport Wi-Fi networks are not safe by default — and never will be. They’re convenient, free, and ubiquitous, which is what makes them attractive to attackers. The defense isn’t avoiding them; it’s making them safe to use through a small set of habits anchored by a reputable VPN.
Confirm the network name with staff. Run the VPN. Watch the captive portal carefully. Use HTTPS-only mode. Switch to cellular for genuinely sensitive activity. Forget the network on the way out.
Want to keep training the awareness that catches the next variation? Try a quick round of Cyber Trivia — many questions cover Wi-Fi and network attacks directly — or subscribe to the Making Sense of Security newsletter for ongoing security briefings designed for travelers, families, and small-business owners. Travel safe, log in safer.